OTP Brute Force Attack and Rate Limiting – Simple Explanation
Today, almost every application uses OTP for security. Banking apps, payment apps, social media platforms, and email logins all depend on OTPs. We usually believe OTPs are fully secure, but this is not always true. If the system behind OTP verification is weak, attackers can misuse it.
What is an OTP?
OTP stands for One-Time Password. It is a temporary code sent to a user to verify their identity. An OTP is valid for a short time and can be used only once.
OTPs are commonly used for:
- Login verification
- Password reset
- Payment confirmation
- Account recovery
Most people think OTPs are secure because they are random. But the real problem is not the OTP itself. The problem is how the server handles OTP verification.
What is an OTP Brute Force Attack?
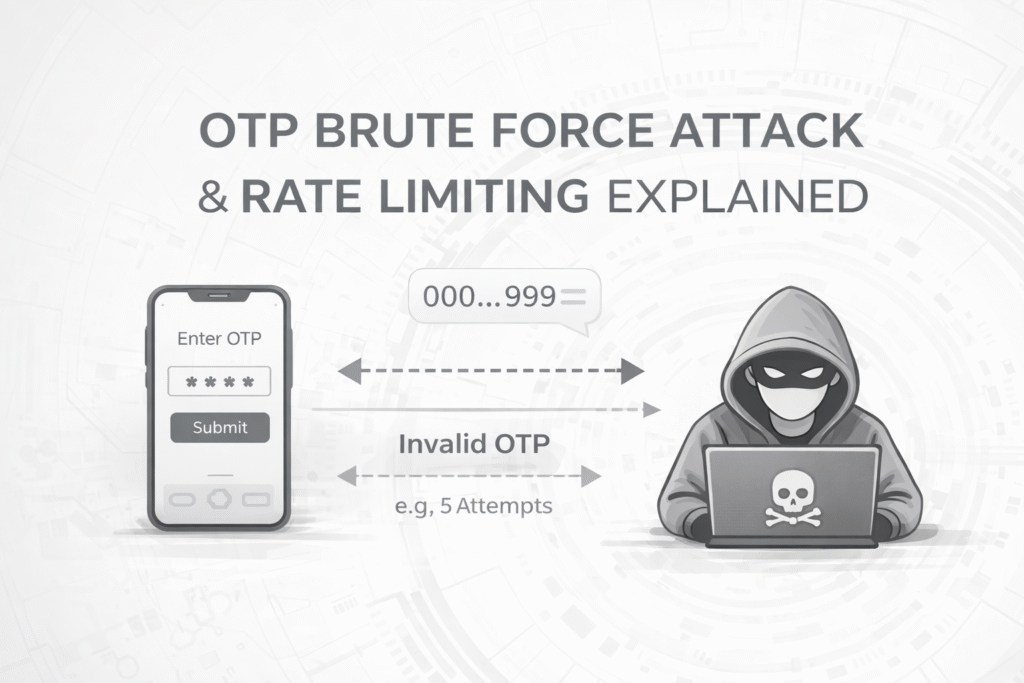
An OTP brute force attack happens when an attacker tries many different OTP values again and again until the system accepts one.
In this attack:
- No code is broken
- No encryption is cracked
- No server is hacked directly
The attacker only checks how many OTP attempts the system allows.
Why Do OTP Brute Force Attacks Work?
OTP brute force attacks work mainly because of missing or weak rate limiting.
Many applications make these mistakes:
- No limit on OTP attempts
- OTP attempts are not tracked properly
- No temporary block after multiple failures
So the weakness is not in the OTP length or randomness, but in the system logic.
What is Rate Limiting?
Rate limiting is a security rule applied by the server. It controls how many requests a user can make in a certain time.
Examples of rate limiting:
- Only 3–5 OTP attempts allowed
- Temporary lock after multiple failures
- Delay added between attempts
Rate limiting protects systems from abuse and automated attacks.
Simple Example of OTP Brute Force
Imagine an app with an OTP verification screen. The user enters the wrong OTP, and the system shows “Invalid OTP”.
If the system allows unlimited OTP attempts, an attacker can keep trying different OTPs very quickly.
Because the server does not stop these attempts, the attacker may eventually guess the correct OTP.
Why Is OTP Brute Force Dangerous?
If an OTP brute force attack is successful, an attacker can:
- Take over user accounts
- Perform unauthorized transactions
- Access private user data
- Cause financial loss
For banking and fintech applications, this can result in serious damage.
This Is a Logic Flaw, Not Traditional Hacking
OTP brute force attacks do not depend on advanced hacking tools. They depend on weak system logic.
The attacker:
- Does not break security
- Does not exploit code bugs
- Only abuses system rules
That is why OTP brute force is considered an authentication failure or a rate limiting failure.
OTP Brute Force and OWASP
OTP brute force issues are related to:
- OWASP Top 10 – Identification and Authentication Failures
- OWASP API Security – Lack of Resources and Rate Limiting
This makes it a high-risk security issue.
How Can OTP Brute Force Be Prevented?
A secure OTP system needs more than just OTP generation.
Best practices include:
- Limit OTP verification attempts
- Apply strict server-side rate limiting
- Temporarily block users after failures
- Monitor suspicious behavior
- Force OTP regeneration after limits
Security is not only about prevention, but also about detection and monitoring.
Ethical and Legal Note
Learning about OTP brute force attacks is important for security awareness. However, testing such attacks without permission is illegal and unethical.
Always use this knowledge only for educational and defensive security purposes.
Conclusion
OTPs are secure only when implemented correctly. If rate limiting and attempt control are missing, even OTP-based systems can fail.
OTP brute force attacks teach us an important lesson: security depends more on logic than on features.
Every developer and cybersecurity learner should take OTP handling and rate limiting seriously.
Disclaimer: This article is for educational purposes only.