In cybersecurity, not every attack depends on breaking encryption or guessing passwords. Some attacks exploit something much simpler but very powerful: timing. One such vulnerability is known as a Race Condition. This vulnerability occurs when multiple users or processes try to access the same resource at the same time, and the application fails to handle these actions safely.
Race Condition vulnerabilities are commonly found in web applications, operating systems, banking platforms, file-handling systems, and APIs. If left unprotected, they can result in unauthorized access, duplicate transactions, data corruption, or even complete system compromise.
What Is a Race Condition?
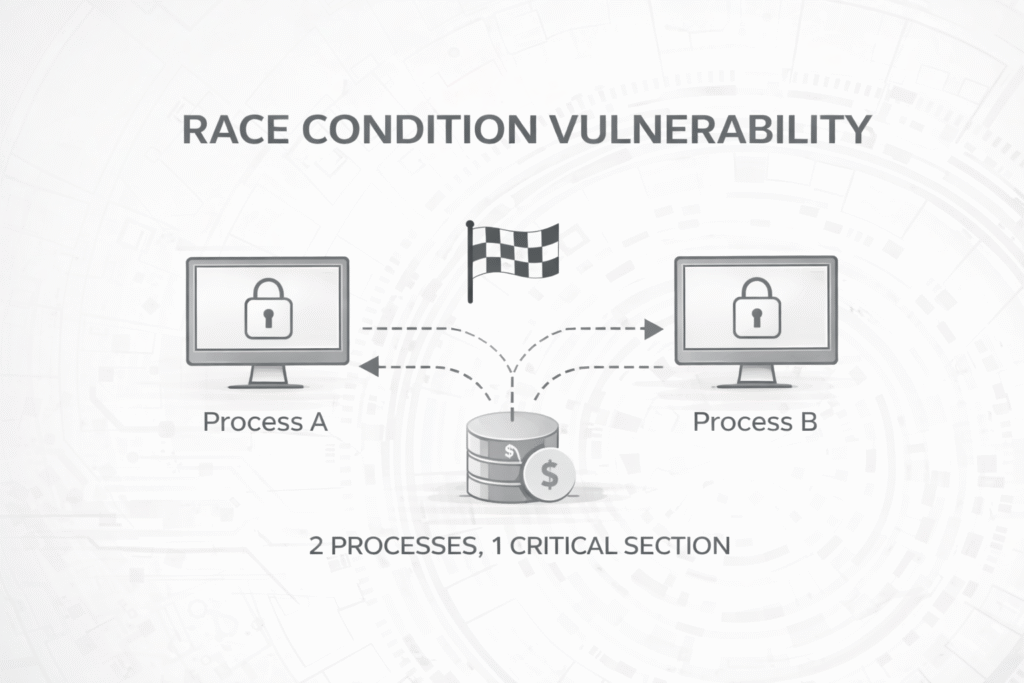
A Race Condition happens when the result of an operation depends on the order or timing of multiple events. If an application assumes that actions will occur one after another, but they actually happen at the same time, a vulnerability is created.
Attackers exploit this by sending multiple requests very quickly, forcing the system to behave incorrectly.
In simple terms:
- Two or more actions access the same resource
- The system does not lock or synchronize access
- The attacker wins the “race” by acting faster
Real-Life Example of a Race Condition
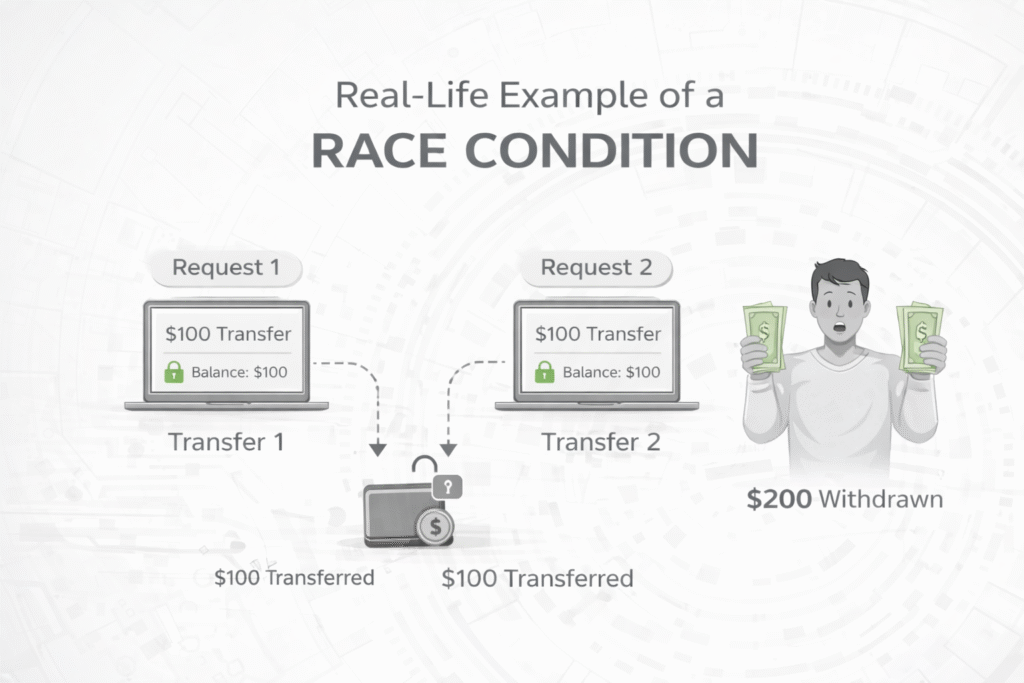
Imagine an online wallet system. Before transferring money, the system checks if your balance is sufficient.
If two transfer requests are sent at the same time:
- Both requests check the balance
- Both see sufficient funds
- Both transfers succeed
As a result, the user withdraws more money than they actually had. This happens because the system failed to lock the balance while processing the first request.
This exact logic flaw is what attackers exploit in real-world race condition attacks.
How Race Condition Attacks Work
Most race condition attacks follow a similar pattern:
- The application performs a security check
- The application performs an action based on that check
- No locking or synchronization is used
- The attacker sends multiple requests simultaneously
Because the system processes these requests in parallel, it cannot distinguish which request should be handled first.
This creates an opportunity for attackers to bypass security controls.
Common Types of Race Conditions
1. Time-of-Check to Time-of-Use (TOCTOU)
This is the most common race condition. It occurs when:
- The system checks a condition (e.g., permission)
- There is a small delay
- The system performs an action assuming the condition is still valid
Attackers exploit the gap between the check and the action.
2. File-Based Race Conditions
These occur when multiple processes read or write the same file. For example:
- Temporary files
- Log files
- Configuration files
An attacker may replace or modify a file before the system finishes processing it.
3. Database Race Conditions
These occur when database operations are not atomic. Common examples include:
- Coupon redemption systems
- Account registration limits
- Voting or like systems
Attackers can exploit these to perform actions multiple times.
Where Race Conditions Are Commonly Found
- Online payment systems
- E-commerce checkout processes
- Login and authentication systems
- Password reset mechanisms
- File upload and download systems
- API rate-limiting logic
Any system that handles concurrent requests without proper controls is a potential target for race condition attacks.
How Attackers Exploit Race Conditions
Attackers use automation tools to send multiple requests at the same time. Instead of clicking buttons manually, they:
- Send parallel HTTP requests
- Use multi-threading
- Exploit server processing delays
The goal is to overwhelm the system and force it to process multiple actions simultaneously.
Even a delay of a few milliseconds can be enough for exploitation.
Impact of Race Condition Vulnerabilities
If exploited successfully, race condition vulnerabilities can lead to:
- Unauthorized financial transactions
- Account takeover
- Privilege escalation
- Data inconsistency and corruption
- Business logic abuse
These vulnerabilities are often rated as high or critical because they directly impact system integrity.
Why Race Conditions Are Hard to Detect
Race conditions are difficult to identify because:
- They depend on timing
- They may not occur consistently
- They are hard to reproduce manually
A system may appear secure during normal testing but fail under high traffic or deliberate stress.
How to Prevent Race Condition Vulnerabilities
1. Use Proper Locking Mechanisms
Locks ensure that only one process can access a resource at a time. This prevents simultaneous execution of critical operations.
2. Use Atomic Operations
Atomic operations complete fully or not at all. Databases provide transactions that help avoid race conditions.
3. Implement Server-Side Validation
Never rely on client-side checks. All validations must be enforced on the server.
4. Rate Limiting
Limit how many requests a user can send in a short period. This makes exploitation much harder.
5. Queue-Based Processing
Critical actions should be placed in queues and processed sequentially instead of in parallel.
Race Conditions in Modern Web Applications
With the rise of APIs, microservices, and cloud-based systems, race conditions have become more common.
Applications today handle thousands of concurrent requests, making synchronization more important than ever.
Developers must design systems assuming that multiple actions can happen at the same time.
Conclusion
Race Condition vulnerabilities are not about complex hacking techniques. They exploit simple logic flaws caused by poor synchronization.
Understanding how race conditions work is essential for:
- Developers building secure applications
- Security testers performing audits
- Bug bounty hunters identifying business logic flaws
By using proper locking, atomic operations, and secure design principles, race condition vulnerabilities can be effectively prevented.
In cybersecurity, timing matters — and even milliseconds can make a difference.